
Reverse Engineering With AI Unearths High-Severity GitHub Bug
Wiz used an AI reverse-engineering tool to pinpoint a vulnerability that previously would have been too costly and time-consuming to undertake.
Aggregated from vendor advisories, security research, and industry publications.

Wiz used an AI reverse-engineering tool to pinpoint a vulnerability that previously would have been too costly and time-consuming to undertake.
ORNL says portable detector kit can separate real GPS signals from fake ones even at equal strength GPS spoofing, which sends fake satellite-like signals, and GPS jamming, which dr…

New research from Enterprise Management Associates (EMA) suggests that the first wave of AI adoption—centered on chatbots and virtual assistants—is succumbing to an AI agent-driven…
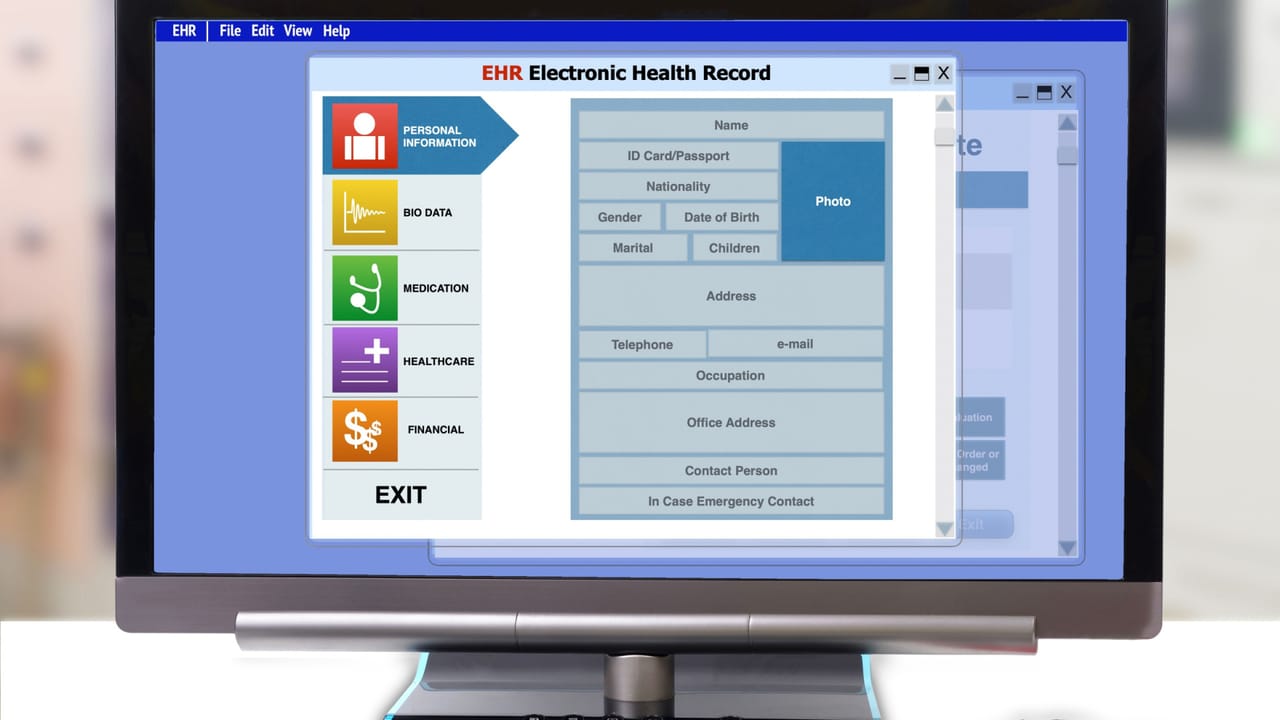
Flaws in OpenEMR's platform — used by more than 100,000 healthcare providers — enabled database compromise, remote code execution, and data theft.
Second try's a charm? Microsoft and the US Cybersecurity and Infrastructure Security Agency (CISA) warned that attackers are exploiting a zero-click Windows flaw that can expose se…
Microsoft readies the axe once again for yesterday's security Microsoft has warned users still clinging to legacy TLS versions that the end is nigh for TLS 1.0 and 1.1 on POP3 and …
Authors say it acquired an LLM that was trained on their copyrighted data, and judge keeps asking for more info Databricks cannot shake a class action lawsuit targeting its LLM, wh…
Kyler and Ned are joined by Enrico Teotti, an independent consultant with over 25 years of experience. Enrico has worked with clients on real-world AI implementations, and he’s her…

IT teams managing multi-vendor networks are dealing with a growing volume of alerts and a shrinking pool of engineers with the expertise to act on them. AI, and more specifically a…
New sealed bootable container images and Stratis storage, too Fedora Linux 44 has arrived – in multiple formats and for several CPU families, including some new container formats a…

Cybersecurity researchers are sounding the alarm about a new supply chain attack campaign targeting SAP-related npm Packages with credential-stealing malware. According to reports …
The emerging ransomware has been deployed against victims of the TeamPCP supply chain attacks, but organizations should think twice before paying for a decryptor.

Cybersecurity researchers have discovered malicious code in an npm package after a malicious package as a dependency to the project by Anthropic's Claude Opus large language model …

An analysis of the destructive malware reveals sophisticated living-off-the-land (LotL) techniques and detailed strategies for the widespread deletion of data.

In February 2026, researchers uncovered a shift that completely changed the game: threat actors are now using custom AI setups to automate attacks directly into the kill chain. We …

Every security team has a version of the same story. The quarter ends with hundreds of vulnerabilities closed. The dashboards are bursting with green. Then someone in a leadership …
That’s a lot. No, it’s an extraordinary number: Since February, the Firefox team has been working around the clock using frontier AI models to find and fix latent security vulnerab…

cPanel has released security updates to address a security issue impacting various authentication paths that could allow an attacker to obtain access to the control panel software.…

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added two security flaws impacting ConnectWise ScreenConnect and Microsoft Windows to its Known Exploite…

In yet another instance of threat actors quickly jumping on the exploitation bandwagon, a newly disclosed critical security flaw in BerriAI's LiteLLM Python package has come under …

The North Korean group is using stolen victim videos, AI-generated avatars, and fake Zoom calls to scale malware attacks against cryptocurrency executives.

Chris Inglis was the head civilian in charge at the NSA when the Snowden leaks exploded. He gets candid about mistakes the organization made, and what CISOs need to know about spot…

When 0APT and KryBit attacked each other, they exposed infrastructure and operational data, giving defenders rare insight into ransomware operations.
The malware has filled the gap created by last year's law enforcement takedowns of Lumma and Rhadamanthys.

Cybersecurity researchers have disclosed details of a critical security vulnerability impacting GitHub.com and GitHub Enterprise Server that could allow an authenticated user to ob…
What separates good Wi-Fi engineers from ones who really can troubleshoot anything? Linux. Understanding Linux—from packet capture workflows to using tcpdump to how USB NIC drivers…

A cybercrime group of Brazilian origin has resurfaced after more than three years to orchestrate a campaign that targets Minecraft players with a new stealer called LofyStealer (ak…

ThousandEyes, a Cisco company, monitors how ISPs, cloud providers and conferencing services are handling any performance challenges and provides Network World with a weekly roundup…
Article URL: https://www.wiz.io/blog/github-rce-vulnerability-cve-2026-3854 Comments URL: https://news.ycombinator.com/item?id=47936479 Points: 447 # Comments: 92
A cryptographically relevant quantum computer is, at some point, going to emerge that can crack modern encryption. But we don’t know when, so it’s tempting to set this problem asid…